 When you are searching for an answer on how to improve your Mac's performance, you might get overwhelmed by the information on some Mac cleaning app websites.
When you are searching for an answer on how to improve your Mac's performance, you might get overwhelmed by the information on some Mac cleaning app websites.
It's not the amount of data but the unknown technical terms that cause the confusion and make you hesitate about buying or downloading the app or looking further.
Fortunately, we have put together a glossary that delivers the basic knowledge you need to understand the universe of Mac cleaning software. In addition to our FAQs, guides and various other articles, this list of terms will make you feel more confident and help you make better decisions when searching for Mac optimization software.
Terms
Adware
The label adware – a shortened version of ‘advertising supported software’ – is applied to any software or application displaying an advertisement. That usually happens through pop-up or pop-under windows, which can be disruptive to some users. Adware is not inherently malicious but it can be annoying. Adware is also considered grayware.
Cache
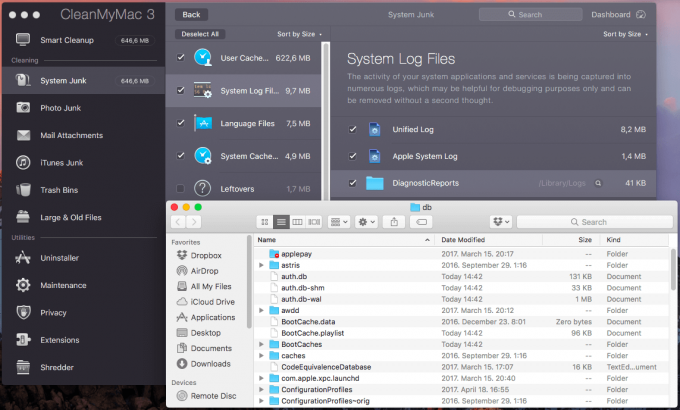
 Your Mac stores different types of temporary files, such as the web browser cache, browsing history, a messaging cache, caches generated by apps or files, partially completed downloads, the system cache and the user cache. Sometimes these files get corrupted because of software updates, causing problems at launch.
Your Mac stores different types of temporary files, such as the web browser cache, browsing history, a messaging cache, caches generated by apps or files, partially completed downloads, the system cache and the user cache. Sometimes these files get corrupted because of software updates, causing problems at launch.
These temporary files aim to help your Mac run faster. For example, if you visit a web page, macOS creates a storage area on your hard drive to hold the most recently downloaded pages. By default, web browsers cache everything from a web page such as documents, images and other content. To enable rapid access, your web browser uses your computer's memory to store recently visited webpages.
The real problem with caches is that they can become corrupt, causing weird problems, hence why deleting them can be an easy fix.
Cookies
Cookies and other data stored on your computer by web browsers includes information that you may have provided – such as your name, email address, and preferences – and they all serve the purpose of identifying the user the next time you return, so the site can provide information that might be of interest. Safari, for example, accepts cookies and website data only from the sites you visit. Removing stored cookie data can reduce tracking, but it is important to note that it will also log you out of websites and possibly change website behavior.
DNS Cache
The DNS cache stores the locations translated into IP addresses of web servers that contain the websites a user has visited. The website becomes unavailable if the location of the web server changes before the entry in the user's DNS cache updates. It is recommended that you flush the DNS cache, especially if a user encounters a number of HTML 404 error codes. Removing the DNS cache will trigger your Mac to request name servers for the new DNS information.
Freemium
Freemium is a pricing strategy used by software developers. Although it is free of charge, it typically has premium features that require a payment should you wish to use all of the software’s functionalities. It has to be differentiated from free and open-source software since freemium software’s source code is typically unavailable.

Freeware
Software that is available for use at no monetary cost. Freeware the abbreviated term for free software.
Grayware
Applications that fall under this classification behave in an annoying manner such as those using pop-up windows, but they are less serious and troublesome than malicious software or malware. Adware, dialers, joke programs, remove access tools and any unwanted files and programs are included in the grayware classification. Broadening the classification, we could say grayware is apps or files that aren't classified as viruses or Trojan-horse programs. We can't say grayware is harmless, because it can negatively affect a computer's performance and the privacy of the user. Spyware and grayware often accesses a corporate network when users download legitimate software that has grayware applications included in the installation package.
iTunes Junk
As central software for iOS devices and media management, iTunes stores various data such as iOS software downloads, iOS device backups, Apple Music cache and iTunes Store cache files. Third party Mac cleaning software will look for these cache folders and older iOS device backups and remove them.
Log Files
The Mac contains a number of log files sent by a variety of applications and system processes, hence these log files contain a lot of information. A regular Mac user would never have a reason to look at them and it is mostly meant for developers, but log files are useful when diagnosing a problem. The location of many logs files is the /private/var/log folder, but you'll find others in /Library/Logs, and those generated by user applications are in each user's /Library/Logs folder.
Maintenance Scripts
Every Mac includes a self-healing feature called maintenance scripts. There are three maintenance scripts your Mac automatically runs in the early morning hours between 3am and 5am local time, if possible. If not, it runs these scripts shortly after it is powered on. The first are daily scripts, which delete some temporary files and record various statistics.
The weekly scripts rebuild the ‘locate’ and ‘whatis’ databases. Depending on the version of macOS , weekly scripts also rotate various log files such as ftp.log, lookupd.log, lpr.log, mail.log, netinfo.log, ipfw.log, ppp.log, and secure.log.
The monthly scripts rotate some minor log files and record user statistics. While the possibility of these scripts not running as scheduled is very low, if they don't run for an extended time, extra space may be taken up on your Mac computer.
Malware
 All software and files that are harmful to a computer user are defined as malware, the abbreviated term for malicious software. This includes computer viruses, worms, Trojan horses and even spyware.
All software and files that are harmful to a computer user are defined as malware, the abbreviated term for malicious software. This includes computer viruses, worms, Trojan horses and even spyware.
Any of these programs can perform various functions, such as stealing, encrypting or even removing sensitive data, altering or hijacking some computing functions, and can track a user's activity on the computer without their permission.
Photos Cache
A useful feature of the Photos app for Mac is its ability to not store the user's photo library on the computer; iCloud instead dynamically loads and unloads as the person uses it. That helps the user manage Mac storage. Still, in order for this feature to function, Photos needs to store thumbnail data for every item the user has in the photos library. macOS actually generates two thumbnail files for every image: a 1024 pixel image and a standard 480×350 thumbnail.
Macs store the photos cache in the ~/Library/Containers/com.apple.cloudphotosd folder. This folder is used for both temporary storage and local storage for shared iCloud images. Even if Photos is set to optimize videos and images, shared iCloud albums remain cached at full resolution. Depending on the number of shared iCloud albums, this folder can occupy various amounts of precious disk space on your Mac.
Rebuild Launch Services Database
Files are designed to be opened with a specific app, which we call default apps. Still, a user has the option to select another app to open a specific type of file. For example, a .docx file opens with Microsoft Word by default but a user can select Apple's Pages app to open that file with the “Open With” command. However, this can get out of control, such as seeing old versions of apps on the list of compatible software when opening a particular file type. To address this issue, the user needs to reset macOS's LaunchServices database. That script is called Rebuild Launch Services Database.
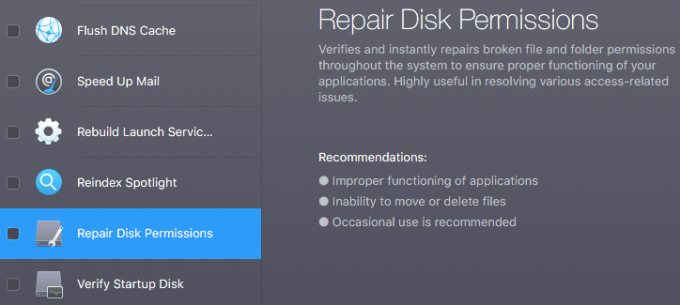
Repair Disk Permissions
Disk permissions are file settings that influence the ability to read, write or run a file. That can change in time and if permissions aren't set correctly, it affects the performance of the software using it. Mac cleaning and optimization applications include scripts that repair disk permissions, but macOS has its own utility software that does the same: Disk Utility. However, beginning with El Capitan OS X 10.11, the twelfth major release of macOS (formerly OS X), system file permissions are automatically protected. It's no longer necessary to verify or repair permissions with Disk Utility.
Scareware
A form of malware, scareware uses social engineering to cause the perception of threat to manipulate the user into buying or downloading unwanted software. Users browsing the web, for example, are presented with a tempting offer, such as a ‘free security scan’, typically through a pop-up window or an email. The free scan usually claims to find a variety of problems, and within seconds users are bombarded with urgent pop-ups urging them to buy security software. In reality, there is nothing to fix, but scareware developers exploit users' fear of online viruses and security threats. The problem with these types of apps are that they are downloaded as a quick fix but can, in fact, become harmful.
Spyware
Included in the malware category and one of the hardest to detect is spyware. It collects private information about the user such as web browsing habits, browsing history or sensitive financial information like credit card numbers, and uses the internet to send this data to third parties without the user's knowledge. Keylogger apps, which track the keys you type on your computer, are also considered spyware. Still, that doesn't mean all software that tracks your online activity or presents targeted ads is bad. For example, if you sign up for a free service, sometimes you ‘pay’ for it by agreeing to be tracked and receive targeted ads.
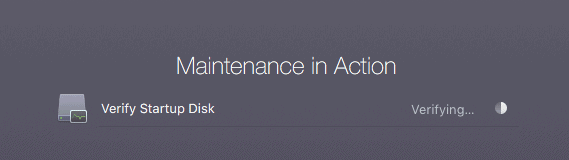
Verify Startup Disk
Third party Mac cleaning apps and macOS's built-in tool Disk Utility can check the health of the Mac's startup disk. For example, if a user encounters various problems such as multiple apps quitting unexpectedly, a file is corrupted, an external hard drive isn’t working as it should or the Mac won't start up, that's a sign that the startup disk is faulty. Third party Mac optimization applications will prompt the user to verify the startup disk to check the status of the disk. If issues are detected, Apple recommends using Disk Utility to repair the startup disk.
Virus
One of the most common types of malware. Macs are considered more secure than Windows computers; malware developers are less likely to target Mac users because macOS accounts are worth a far smaller market share than Windows. macOS is Unix-based and offers a number of security features built in. On top of that Apple has included a number of security measures to protect Macs from viruses such as Gatekeeper, which blocks software that hasn’t been digitally signed and approved by Apple. Still, the risk is there and from time to time Mac users have become targets of malware attacks.
Best Mac Optimization Software of 2024
| Rank | Company | Info | Visit |
|
1
|
 |
|
|
|
2
|
 |
|
|
|
3
|
 |
|
Get the Best Deals on Mac Optimization Software
Stay up to date on the latest tech news and discounts on Mac optimization software with our monthly newsletter.