 Developed with newer storage technologies in mind – in particular SSD – and designed to address the faults of the dated HFS+ that was used in Mac OS Extended, the Apple File System or APFS packs in appealing new features such as point-in-time snapshots and more. When it launched in the fall of 2017, every Mac compatible with macOS 10.13 High Sierra and equipped with an SSD was automatically migrated to the new file system. But the transition from HFS+ wasn't that smooth, since APFS included several nasty bugs.
Developed with newer storage technologies in mind – in particular SSD – and designed to address the faults of the dated HFS+ that was used in Mac OS Extended, the Apple File System or APFS packs in appealing new features such as point-in-time snapshots and more. When it launched in the fall of 2017, every Mac compatible with macOS 10.13 High Sierra and equipped with an SSD was automatically migrated to the new file system. But the transition from HFS+ wasn't that smooth, since APFS included several nasty bugs.
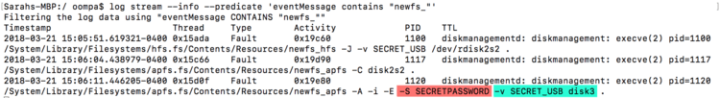
Log Files Leaking APFS Encrypted External Volumes' Password
A severe security flaw exposes passwords of encrypted APFS-formatted external drives. Discovered by computer forensic expert Sarah Edwards, the passwords are displayed in plain text in the unified logs. This means that anyone with physical access to the Mac is able to obtain that data. Furthermore, if the cyber criminal develops malware with the purpose of collecting such data, this can be done remotely as well.
Edwards has tested various versions of macOS 10.13 High Sierra but the bug still wasn't addressed by the time of writing with the macOS 10.13.3 update.
Disk Utility Bug Exposes Password of Encrypted APFS Volumes
A nasty bug hidden within Disk Utility exposed the passwords of encrypted APFS volumes in plain text on macOS 10.13 High Sierra. After adding an encrypted APFS volume to a container, setting a password hint, and then unmounting and remounting the volume, Brazilian developer Matheus Mariano discovered that by clicking on the “Show Hint” button, Disk Utility displayed the password instead of the hint.
He couldn’t replicate the issue following the same steps using Terminal commands, and Apple addressed the Disk Utility security flaw with the macOS 10.13 Supplemental Update.
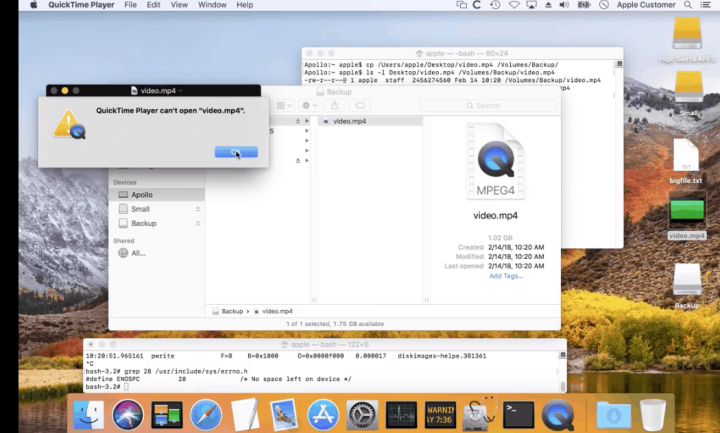
Disk Image Flaw in APFS Could Lead to Loss of User Data
A serious bug affecting APFS-formatted sparse disk images passed unnoticed by Apple and thousands of developers: despite being completely full, a sparse disk image would show ample free space. These types of files are used for various purposes ranging from backups to network volumes and this is how Carbon Copy Cloner developer Mike Bombich became aware of the issue and notified Apple about it.
Briefly put, a sparse disk image allows users to add as much data as the underlying disk permits. In other words, if you created a sparse disk image with a capacity of 256GB on a volume that permits 256GB and you then added 200GB of data to the latter, the disk image would show only 56GB of free space to reflect the change in capacity.
Due to a bug in Apple's new file system, however, APFS-formatted sparse disk images don't properly reflect that. Instead, they create the illusion of lots of free space, which leads to data loss if the file(s) moved to the disk image exceed its real capacity. The copy process won't give any errors either, but any affected files will become corrupted because they won't actually end up on the sparse disk volume.
This bug only affects sparse disk images, so regular users won't run into this error with an APFS-formatted startup volume.
One More Thing…
APFS apparently surprised Geniuses as well, which Charles Arthur, formerly of The Guardian, experienced with his machine running macOS 10.13 High Sierra. Since Geniuses are Apple employees dealing with hardware or software issues affecting the company's products, this is something you wouldn’t expect from the world's biggest tech company.
Instead of booting from a networked drive running the latest operating system, the Genius dealing with Arthur's issue booted his Retina MacBook Pro from a macOS 10.12 networked drive.
Because HFS+ formatted drives can’t read files encoded in APFS, this triggered additional issues that would never have happened if Apple had updated their procedures to take users of the new file system into consideration.
Have you encountered any issues since migrating to APFS? If so, let us know in the comments section below.
Best Mac Optimization Software of 2024
| Rank | Company | Info | Visit |
|
1
|
 |
|
|
|
2
|
 |
|
|
|
3
|
 |
|
Get the Best Deals on Mac Optimization Software
Stay up to date on the latest tech news and discounts on Mac optimization software with our monthly newsletter.

Joao says
I have an external 2″5 HDD drive, a 5TB seagate, which has one partition formatted with APFS. The formatting is encrypted with a case sensitive file system.
After moving files around a lot (sometimes simultaneously), the disk sometimes becomes inaccessible. The partition is still there, but it can’t be read. The only thing to be done at this point is to reformat the partition.
This is happening with MacOS Monterey, 12.6, both with intel silicon and the M1 MacBook Pro.